Crackonosh virus mined $2 million of Monero from 222,000 hacked computers
A previously undocumented Windows malware has infected over 222,000 systems worldwide since at least June 2018, yielding its developer no less than 9,000 Moneros ($2 million) in illegal profits.
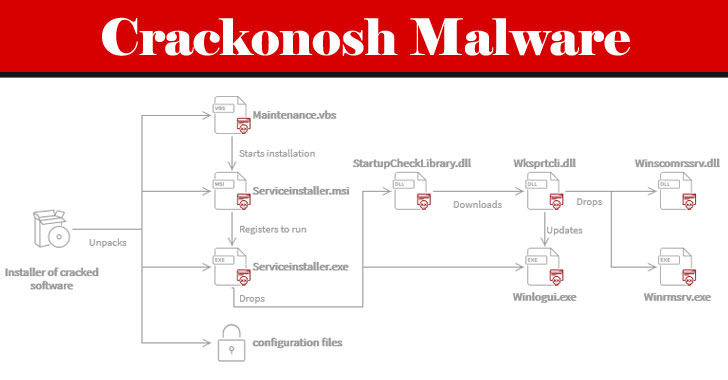
Dubbed “Crackonosh,” the malware is distributed via illegal, cracked copies of popular software, only to disable antivirus programs installed in the machine and install a coin miner package called XMRig for stealthily exploiting the infected host’s resources to mine Monero.

As part of its anti-detection and anti-forensics tactics, the malware also installs its own version of “MSASCuiL.exe” (i.e., Windows Defender), which puts the icon of Windows Security with a green tick to the system tray and runs tests to determine if it’s running in a virtual machine.
Last December, security researcher Roberto Franceschetti disclosed that antivirus applications could be disabled by booting into safe mode and renaming their application directories before their corresponding services are launched in Windows.
Microsoft, however, said the issue doesn’t “meet the bar for security servicing,” noting that the attack is predicated on having administrative/root privileges, adding a “malicious administrator can do much worse things.”